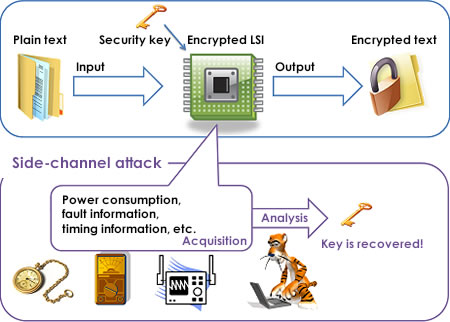
Cryptography | Free Full-Text | Power Side-Channel Attack Analysis: A Review of 20 Years of Study for the Layman

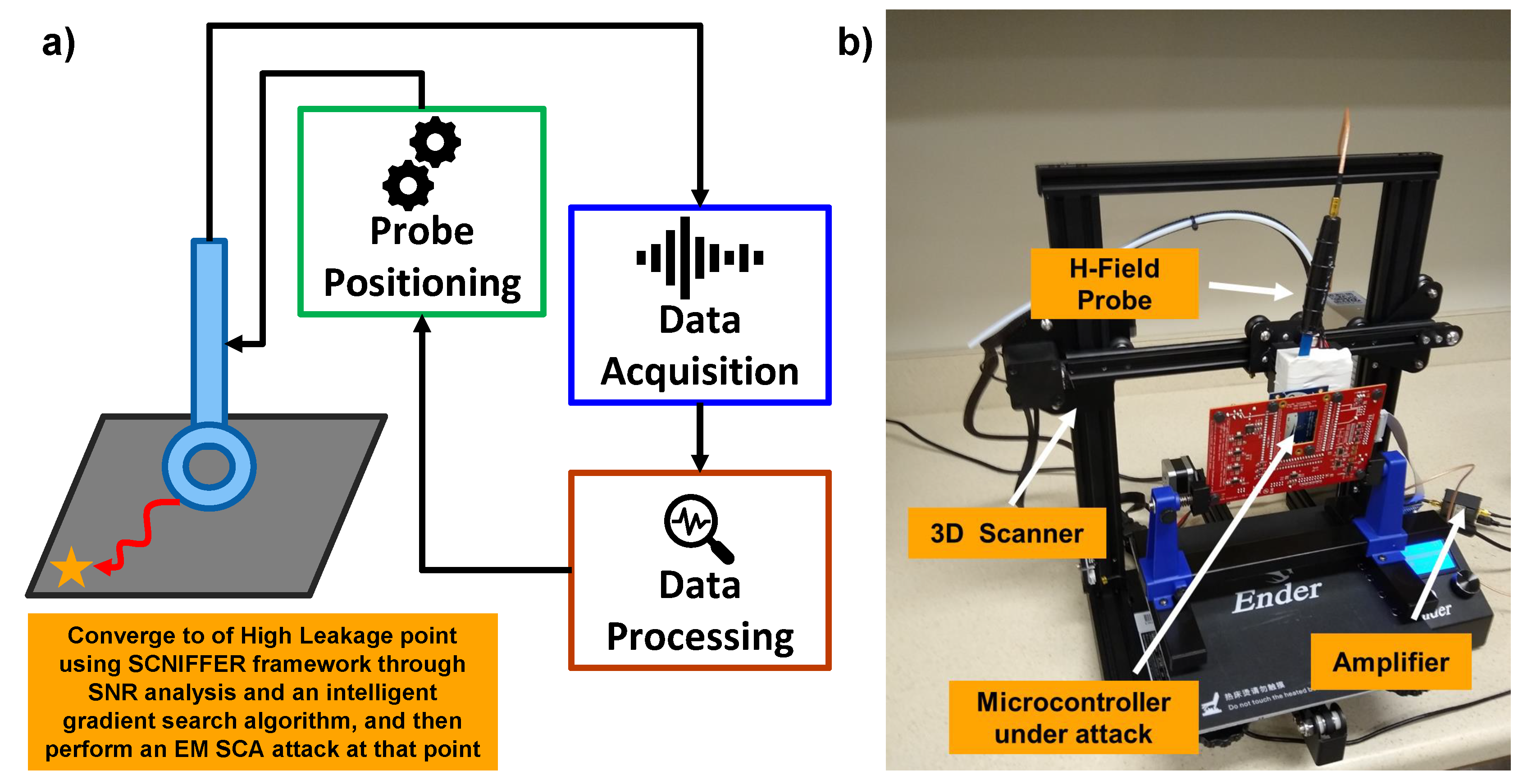
A survey of electromagnetic side-channel attacks and discussion on their case-progressing potential for digital forensics - ScienceDirect
High Efficiency Power Side-Channel Attack Immunity using Noise Injection in Attenuated Signature Domain
Side-Channel Attacks: Ten Years After Its Publication and the Impacts on Cryptographic Module Security Testingª